Intro: Why Data Center Security Best Practices is a Board-Level Problem Now
Most enterprises don’t lose data because their enterprise-grade, high-cost firewalls failed; they lose it because someone propped open a server room door, left a privileged account active after an employee departure, or ran a flat network where a compromised VM could reach production storage. Data center security best practices exist precisely to close those seemingly small but catastrophic gaps — systematically, before an incident force the conversation.
The risk surface has expanded sharply. IBM’s 2024 Cost of a Data Breach report put the global average breach cost at $4.88 million, the highest ever recorded. Meanwhile, hybrid architectures have blurred the perimeter: workloads now span on-premises racks, colocation cages, and cloud regions simultaneously, and each transition point is a potential exposure. Data center compliance standards like ISO 27001 and SOC 2 have evolved to reflect this reality, but many enterprises are still catching up.
This guide walks through the full security stack: physical controls, network and cyber architecture, monitoring and data center risk management, compliance frameworks, and hybrid cloud considerations. At the end, you will find a practical data center security checklist for enterprises you can use to assess your own environment.
Aptly Technology helps enterprise and hyperscale operators build and run data center infrastructure security across the full lifecycle, from commissioning through continuous operations. But the principles below apply regardless of who operates your facility.
What is Data Center Security in 2026 and Why it Matters?
At its core, data center security is the set of physical, technical, and procedural controls that protect the infrastructure hosting your most critical applications and data – from racks and power to hypervisors and GPU clusters.
In 2026, this means combining layered physical protection, modern data center cybersecurity, compliance-driven process, and continuous monitoring into one coherent system rather than scattered, siloed tools.
Typically, a serious enterprise or hyperscale environment in 2026:
- Exceeds 5000 servers and 10 MW of critical IT load, often much more.
- Lives on a multi-building campus with its own fiber, power infrastructure, and high-density rack layouts.
- Runs hybrid: private data center racks, colocation cages, and cloud regions working together for capacity, resilience, and AI workloads.
The board-level question is no longer just “Are we compliant?” but “What are the tip risks in data centers today, and how do companies secure sensitive infrastructure at this scale?” – this guide offers a strategy-level answer to that.
Check our Data Center buildout guide: Click Here!
Physical Security in Data Centers: The Foundation That Cannot Be Skipped
Physical security in data centers is the bedrock of every other control layer. Encryption, firewalls, and identity policies all become significantly weaker if an unauthorized person can walk up to a rack or plug into a console. Physical access is the attack vector that bypasses most logical controls entirely, thus, making data center security solutions program starts here.
Access Control Systems:
Modern access control systems in enterprise data centers run on layered, zone-based principles: facility perimeter, lobby/reception, data hall, and individual caged or colo suites. Each layer requires independent authentication. Data Center security best practice means combining at minimum two factors, proximity badge plus PIN or biometric — at the cage or floor level.
Uptime Institute’s Global Data Center Survey consistently identifies tailgating (piggybacking on an authorized entrant) as one of the most common physical security failures. Mantrap vestibules, where one door must close before the next opens, are the standard mitigation for Tier III and above facilities.
Surveillance Monitoring and Intrusion Detection:
Closed-circuit surveillance monitoring should cover all entry/exit points, server aisles, and loading docks with no blind spots. Video retention of 90 days or more is typical for enterprises under regulatory scope. The footage is only useful if someone is watching it, automated motion detection and alerting after-hours access events is the operational standard, not passive recording alone.
For intrusion detection at the physical layer: alarmed doors with tamper-evident seals on critical cabinets, vibration sensors on raised-floor tiles near high-value racks, and perimeter detection (PIR sensors, fence intrusion) for standalone campus facilities. NIST SP 800-116 provides the federal reference framework for physical access control systems, which many enterprise standards mirror.
Together, these measures are how enterprises prevent data breaches in data centers that would otherwise come from something as simple as an unattended door.
Network Security in Data Centers: Layering Cyber Controls from the Perimeter In
Data center cybersecurity is not a single product or policy — it is a stack of overlapping controls, each designed to limit what an attacker can do after they have defeated the layer above. Network segmentation is where that stack starts.
Robust network security in data centers starts with segmentation and builds from there into encryption, IAM, and zero trust.
Segmentation, Firewalls, and Microsegmentation:
The baseline architecture separates management traffic, storage replication, and production workload traffic onto distinct VLANs or segments, with firewall protection enforcing policy at each boundary. But east-west traffic — server to server, within the same network segment — is where modern attacks move after initial compromise. Microsegmentation addresses this by applying workload-level policies that restrict lateral movement even within a trusted zone.
For hyperscale and AI cluster environments, network security in data centers extends to the GPU fabric layer: InfiniBand and RoCE networks used for AI training require their own isolation and authentication controls, separate from the standard Ethernet management plane.
Encryption Protocols and Data Protection
Encryption protocols are a core part of data center security best practices and apply at two distinct layers. Data in transit should be protected with TLS 1.2+ for management interfaces and application traffic; storage replication traffic between sites should use IPsec or MACsec at the network layer. Data at rest in shared storage arrays or NVMe drives should use AES-256 encryption with keys managed externally to the encrypted volumes, thus keeping encryption keys and the data they protect on the same system removes most of the protection value.
Identity and Access Management (IAM) and Privileged Access
Identity and access management (IAM) controls who can log in to what, from where, and under what conditions. In a data center context this means strict role-based access control (RBAC) for out-of-band management interfaces (BMC/iDRAC/iLO), hypervisor consoles, and storage admin portals, all of which are common targets precisely because they are powerful and often poorly monitored.
Privileged Access Workstations (PAWs) and just-in-time access provisioning — where admin accounts are activated only for the duration of a specific task and automatically revoked — have become standard in mature enterprise environments. These patterns are among the most effective data center security solutions for stopping insider misuse and credential-theft-driven attacks.
Zero Trust Architecture in Data Centers
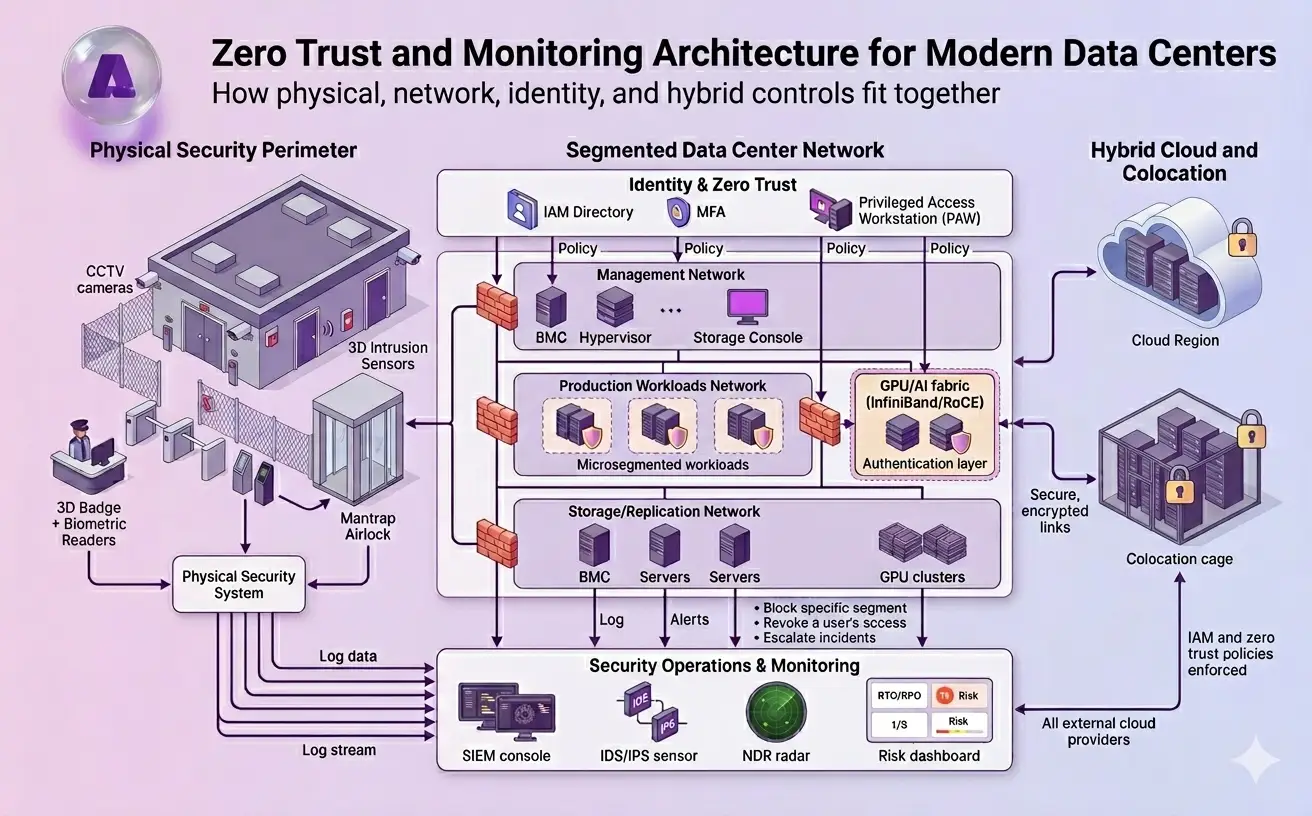
Zero trust architecture replaces the implicit trust that flows from being ‘inside the network’ with explicit, continuous verification of every connection. In a data center context, that means: every workload must authenticate before it can communicate with any other workload; every privileged session is recorded; and network policies default to deny-all unless a specific policy explicitly permits traffic. Another significant part in an enterprise strategy for data center security best practices
NIST SP 800-207 is the authoritative reference for zero trust architecture. The practical implication for data center operators is that zero trust is not a single product you buy, it is a design principle that requires changes to network architecture, identity systems, and operational processes simultaneously.
Monitoring, Threat Detection, and Data Center Risk Management
Controls prevent what they can. Threat detection systems catch what controls miss. The operational reality of modern data center security is that some percentage of attacks will succeed in breaching the perimeter, what matters is how quickly you detect them and how effectively you contain the damage.
SIEM, IDS/IPS, and Network Detection and Response
A Security Information and Event Management (SIEM) platform aggregates logs from physical access systems, network devices, servers, and hypervisors into a unified detection surface. Intrusion Detection/Prevention Systems (IDS/IPS) monitor packet-level traffic for known attack signatures and behavioral anomalies. Network Detection and Response (NDR) platforms like Darktrace or ExtraHop take this further, modeling normal baseline behavior for every device on the network and flagging deviations, which catches attackers using legitimate tools and credentials that signature-based systems miss.
Log aggregation across physical and logical layers is underrated. Correlating a badge-access event at 2am with an unusual login to a storage management console thirty seconds later is the kind of signal that prevents a quiet breach from becoming a disclosed incident. That correlation only works if both systems feed the same SIEM.
Data Center Risk Management and Risk Assessment
Data center risk management is a recurring operational process, not a one-time audit. The data center risk assessment steps that mature organizations run annually, and after any significant infrastructure change, typically follow this sequence:
- Asset inventory: what exists, what it connects to, what data it holds.
- Threat modeling: which threat actors are realistic given your industry and data profile.
- Vulnerability assessment: what technical and process gaps exist relative to those threats.
- Risk scoring: likelihood × impact, using a consistent methodology (e.g., NIST RMF or FAIR).
- Remediation roadmap: prioritized actions with owners and timelines, not a list of findings that ages in a spreadsheet.
Risk management also feeds disaster recovery planning directly. Recovery Time Objectives (RTOs) and Recovery Point Objectives (RPOs) should be set based on actual risk scoring, not guesswork — and tested through live failover exercises at least annually.
Aptly Technology’s 24/7 Monitoring and Operations
For enterprises that do not want to build this monitoring and risk machinery alone, Aptly Technology operates 24/7 Global Operations Centers that watch both physical and cyber telemetry across data centers and GPU clusters in real time. Aptly’s managed services combine SIEM, NDR, and infrastructure health monitoring into one operations layer, turning logs and alerts into concrete actions that reduce dwell time and enforce your data center security best practices continuously.
To see how Aptly embeds security-by-design and round-the-clock monitoring into hyperscale and enterprise environments, visit Aptly’s managed data center services page here.
What Is Data Center Compliance and Why Does It Matter for Enterprises?
Data center compliance standards define the minimum-security controls that a data center must operate to satisfy regulatory, contractual, or industry requirements. They matter for two practical reasons: they reduce the risk of a breach by mandating a baseline of controls, and they reduce the legal and financial exposure when a breach still happens.
Key Compliance Frameworks:
ISO/IEC 27001 is the most widely recognized international standard for information security management systems (ISMS). It does not prescribe specific controls but requires organizations to identify risks and implement controls proportionate to them, making it applicable across industries and geographies.
SOC 2 Type II (developed by the AICPA) audits an organization’s controls around security, availability, processing integrity, confidentiality, and privacy over a defined period, typically 6 to 12 months. For cloud service providers and data center operators, SOC 2 Type II is often a contractual requirement from enterprise customers.
PCI DSS applies wherever payment card data is processed, stored, or transmitted. Its physical and logical security requirements are among the most prescriptive in any compliance framework, including strict segmentation of cardholder data environments, access logging, and annual penetration testing.
Regional regulations, GDPR in the EU, HIPAA in the U.S. healthcare sector, and India’s Digital Personal Data Protection Act (DPDPA), add jurisdiction-specific requirements on top of these baseline frameworks. Most enterprise legal teams now maintain a compliance matrix that maps each regulation’s requirements to specific data center controls.
Cloud and Data Center Security in Hybrid Environments
The clean boundary between ‘on-prem’ and ‘cloud’ does not exist in most enterprise environments anymore. Cloud and data center security now means securing workloads that span private data center racks, colocation cages, and public cloud regions — often with data flowing between all three in real time.
The security challenge in hybrid environments is consistency. IAM policies, encryption key management, and network segmentation controls that work inside your data center need equivalent enforcement in the cloud region where your workloads are replicated. Most cloud security incidents are not cloud provider failures — they are misconfigurations applied to cloud environments that would have been caught immediately in a physical facility with a configuration management process.
Enterprise data protection strategies for hybrid environments typically combine: geo-redundant backup with automated integrity verification; cross-site encryption key management (using hardware security modules, or HSMs, not software-based key stores); and unified IAM that extends from on-premises Active Directory or Okta into cloud identity providers via federation, so that an account is deprovisioning triggers consistently across both environments.
For organizations running AI workloads, the GPU cluster layer adds a specific hybrid security consideration: model weights, training data, and inference endpoints each carry different data sensitivity profiles, and each requires its own access and encryption policy — not a one-size-fits-all approach applied to the whole AI environment.
Data Center Security Checklist for Enterprises
Use this data center security checklist for enterprises as a structured assessment tool — not a compliance checkbox exercise, but a practical framework for finding where your security posture diverges from what mature organizations operate. Map each item to an owner and a current status.
| Category | Control | Maturity Benchmark |
|---|---|---|
| Physical Security | Multi-factor access control at all entry zones | Biometric + badge at cage level; mantrap at data hall entry |
| Physical Security | CCTV with 90-day retention and automated alerting | No blind spots; motion-triggered alerts for after-hours access |
| Physical Security | Intrusion detection on doors, cages, and perimeter | Alarmed seals on high-value cabinets; PIR sensors in aisles |
| Network & Cyber | Network segmentation (management, storage, production) | Separate VLANs; firewall at each segment boundary |
| Network & Cyber | Microsegmentation for east-west traffic control | Workload-level policies; lateral movement blocked by default |
| Network & Cyber | Encryption for data in transit and at rest | TLS 1.3+ in transit; AES-256 at rest; external key management |
| Identity & Access | Role-based IAM with privileged access management | Just-in-time provisioning; PAWs for admin sessions |
| Identity & Access | Zero trust architecture across workloads | All traffic authenticated; default deny; session recording |
| Monitoring & IR | SIEM with cross-layer log correlation | Physical + logical logs unified; mean detection time < 1 hour |
| Monitoring & IR | IDS/IPS and NDR for behavioral detection | Signature + behavioral; tuned to suppress noise below 5% |
| Monitoring & IR | Incident response plan with live failover testing | Tested annually; RTO/RPO validated against risk scores |
| Compliance | ISO 27001 or SOC 2 Type II certification | Current certification; annual audit cycle |
| Compliance | Regulatory mapping (GDPR, HIPAA, PCI DSS as applicable) | Compliance matrix maintained; data classification applied |
| Hybrid Cloud | Unified IAM across on-prem and cloud environments | Federated identity; deprovisioning triggers in all environments |
| Hybrid Cloud | Geo-redundant backup with integrity verification | Cross-region; automated restore testing quarterly |
| Column 1 Value 16 | Column 2 Value 16 | Column 3 Value 16 |
Conclusion: A Secure Data Center Is a System, not a Checklist
The most common mistake in data center security is treating it as a compliance project — do the audit, get the certification, repeat next year. That approach produces a facility that passes inspections and fails incident response.
A genuinely secure data center is a layered system where physical security in data centers and data center cybersecurity reinforce each other, continuous monitoring closes the gap between what controls prevent and what attackers still attempt, and data center risk management keeps the whole system calibrated against an evolving threat landscape.
What that looks like in practice:
- Multi-layer physical access with biometrics and mantrap entry, not just key-card swipe.
- Zero trust network architecture with Microsegmentation, replacing flat networks that make lateral movement trivial.
- Unified IAM and privileged access management that spans on-premises and cloud environments.
- SIEM and NDR run continuously, with cross-layer log correlation, not just compliance log archiving.
- Annual risk assessments using a structured methodology, with findings tracked to resolution, not filed and forgotten.
- Compliance frameworks (ISO 27001, SOC 2, PCI DSS) used as a floor, not a ceiling.
If you are reviewing your own environment against this framework and finding gaps, the data center security checklist above is a practical starting point. Maturing toward zero trust and continuous monitoring is a multi-year program, but every organization must start somewhere.
Aptly Technology’s managed data center operations are built around security-by-design from day one — certified to ISO/IEC 42001:2023, with 24×7 Global Operations Centers and infrastructure security practices validated at hyperscale. If you are evaluating your enterprise data protection strategies or planning a new secure data center architecture, contact Aptly to discuss how we operate security at scale.
See also: GPU Datacenter Buildout Services, AI Infrastructure Managed Services, Managed Data Center Services
Frequently Asked Questions (FAQ):
- What are the best practices for data center security?
- Data center security best practices combine physical controls (layered access, CCTV, intrusion detection), cyber controls (segmentation, encryption, IAM, zero trust), continuous monitoring via SIEM and NDR, and regular risk assessments tied to a compliance framework. The distinguishing factor in mature organizations is that these controls are operated as an integrated system, not maintained as separate silos under different teams.
- How do you secure a data center from cyber attacks?
- The most effective defense combines network segmentation to limit lateral movement, Microsegmentation at the workload level, zero trust authentications for all privileged access, and behavioral detection systems (NDR/SIEM) that flag anomalies before they become breaches. Regular penetration testing and vulnerability scanning should validate that those controls hold up against realistic attack scenarios, not just compliance audits.
- What frameworks apply to data center compliance?
- The core compliance frameworks for enterprise data centers are ISO/IEC 27001 (international ISMS standard), SOC 2 Type II (service organization controls), and PCI DSS (payment card environments). Regional regulations layer on top: GDPR for EU-resident data, HIPAA for U.S. healthcare, and DPDPA for India. Most enterprises maintain a cross-mapped compliance matrix so that a single control set satisfies multiple frameworks where requirements overlap.
- What are common data center vulnerabilities?
- The most frequently exploited data center vulnerabilities include: flat or poorly segmented networks that allow east-west lateral movement after an initial compromise; stale privileged accounts that were never deprovisioned after employee or contractor departures; unpatched out-of-band management interfaces (BMC, iDRAC) that are network-accessible; and physical security gaps like tailgating at mantrap-free entry points. ENISA’s data center threat landscape report identifies supply chain tampering and insider threats as the most underappreciated risk categories for enterprise facilities.
- How does zero trust work in data centers?
- Zero trust architecture replaces implicit network-based trust with continuous, explicit verification. In a data center, this means workloads authenticate to each other before any connection is established (not just at the perimeter), all privileged sessions are verified with MFA and recorded, and network policies default to deny-all unless explicitly permitted. NIST SP 800-207 is the reference architecture. Implementation typically requires changes to network design, IAM systems, and monitoring — it is an architectural transition, not a product deployment.
- How does Aptly Technology approach data center security operations?
- Aptly delivers security-by-design across the full data center infrastructure lifecycle. Its 24×7 Global Operations Centers monitor physical and cyber telemetry in unified dashboards, and its managed services include hardened GPU cluster operations, privileged access management, and compliance-aligned change control processes. As the only Microsoft-trusted supplier authorized to build and support third-party hyperscale datacenters worldwide, Aptly’s security model is built for environments where uptime, data integrity, and regulatory compliance are simultaneously non-negotiable.
- For more, visit Aptly’s managed data center services.